Partnering With Bookkeepers Support & Harvey Norman
We are proud to partner with Bookkeepers Support to provide affordable, business-grade cybersecurity and IT solutions for bookkeepers, including sole traders. When you partner with Harvey Norman Technology for Business, you can protect your business and your clients' privacy with affordable, secure, and reliable solutions. With 24/7 monitoring, real-time threat detection, preventative system maintenance, secure backups, recovery management, rapid incident response, and access to a world-class help desk, this partnership provides you peace of mind. You can be confident your business is protected and compliant, so you can focus on managing your business success.
Recent Webinars
Take a look at the recent webinar we recently held exclusively for Bookkeepers Support members.


Free Cyber Security Risk Assessment
As a member of Bookkeepers Support, you can claim a free cyber security risk assessment conducted by one of our cyber security engineers, valued at $499.
This comprehensive report will outline your vulnerabilities and strengths, providing strategies on how to ensure your business and clients personal and financial data are protected by cyber threats.

How We Deliver
- Simplified IT | Enterprise-grade solutions, secure networks, and expert technology services made easy and stress-free
- Proactive Protection | 24/7 monitoring, real-time threat detection, compliance-ready security, and preventative system maintenance
- Cyber Security | Secure backups, recovery management, advanced threat protection, and rapid incident response
- Local Expertise, Nationwide Support | Access to a world class help desk, backed by personalised service and the support of a trusted national brand
Interesting Articles
We've gone ahead and put together some articles that will ensure you have the most up-to-date information at your fingertips.
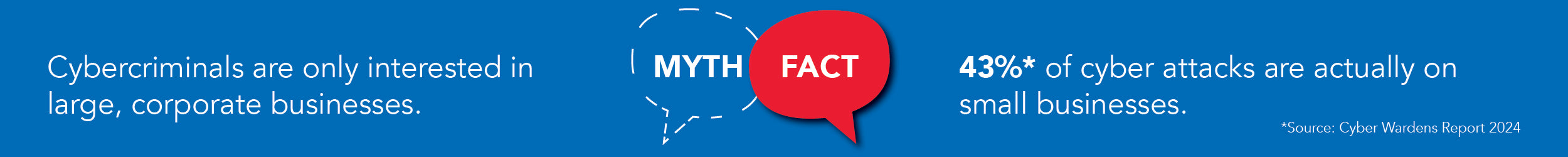
Ultimate Guide to Cyber Security for Small Business Owners

FREE REPORT reveals the Top 6 Cyber Security Threats and how to avoid them
Download your free guide and get a 10-point actionable checklist to implement and start protecting your business today.

With A Trusted Team of Cyber Specialists On Your Side, Your Business Is In Safe Hands
Your sensitive business and client data receive round-the-clock protection from our cutting-edge solutions and highly trained cyber specialists.
By partnering with Harvey Norman Technology for Business, you’ll have access to:
- World-class help desk specialists, backed by a trusted national brand, ready to assist with any IT issue, big or small.
- Reliable solutions from certified and skilled cyber security experts with a proven track record of protecting businesses from cyber attacks.
- A state-of-the-art Security Operations Centre and Network Operations Centre that constantly monitor for threats and vulnerabilities.
We provide proactive, targeted responses, resulting in an enterprise-grade solution at a small business price. That's the peace of mind you get from partnering with Harvey Norman Technology for Business.